The Rising Importance of Quantum Security in Layer-1 Blockchain Roadmaps
An exploration of how quantum computing threats are influencing the security strategies of blockchain networks.
The Slow-Moving Threat that Blockchains Can’t Ignore
Quantum computers may seem like experimental devices: complex setups with unreliable qubits and limited practical use. However, the roadmaps for leading layer-1 blockchains now indicate a significant focus on a new priority: post-quantum security.
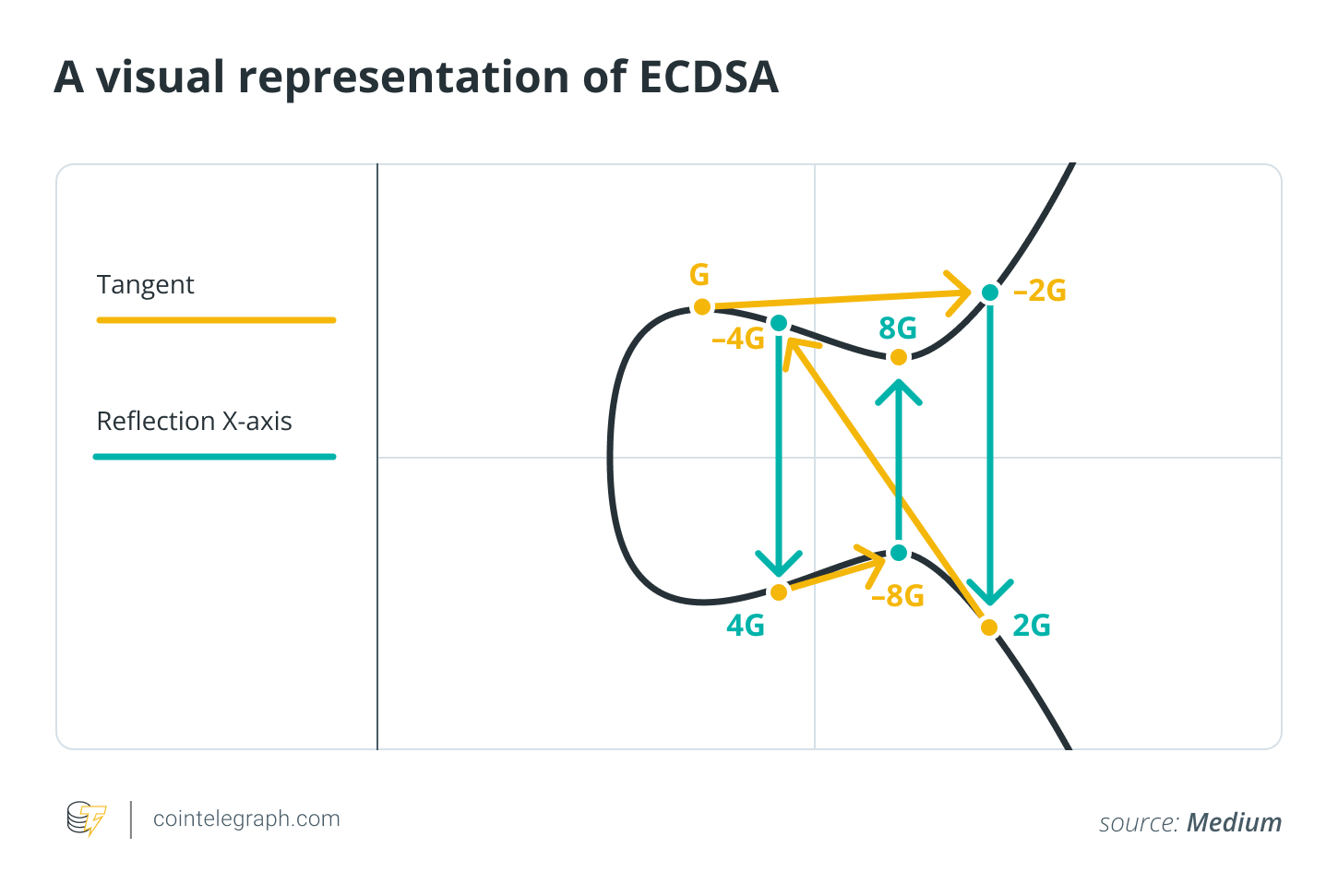
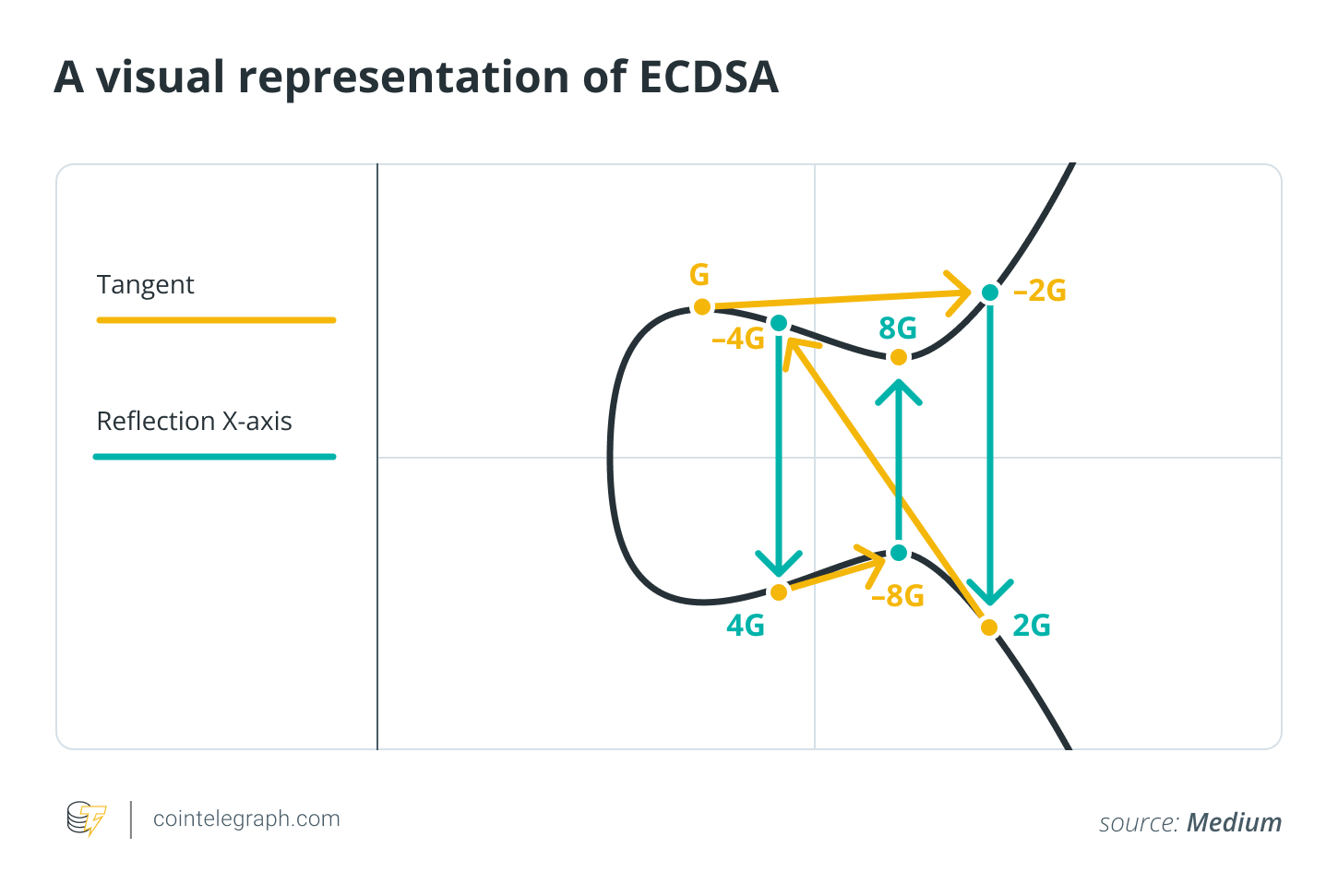
The concern is quite clear, although the mathematics involved can be intricate. Major blockchains utilize elliptic-curve signatures (ECDSA and Ed25519) to verify that a transaction originated from the rightful owner of a private key. In theory, a competent quantum computer executing Shor’s algorithm could potentially uncover these private keys from their public counterparts, allowing malicious actors to generate fraudulent transactions.
 A visual representation of ECDSA
A visual representation of ECDSA
There’s also a “harvest now, decrypt later” perspective. Attackers may collect public blockchain data today and wait until quantum technology advances. As a result, outdated addresses, dormant wallets, and certain smart contract mechanisms could be at risk, even if the networks eventually transition to more secure algorithms.
For long-standing public ledgers that cannot be reset, considering quantum threats is becoming increasingly essential. With the National Institute of Standards and Technology (NIST) releasing formal guidelines on post-quantum standards, and various governments announcing migration deadlines beyond 2030, teams behind layer-1 blockchains are now treating quantum security as a gradual but unavoidable threat.
What Quantum Computers Actually Threaten in Crypto
Quantum computers do not inherently “break blockchains”; instead, they challenge specific algorithms.
The primary concern for cryptocurrencies is public key signatures. Bitcoin, Ethereum, and many other networks depend on elliptic-curve models (ECDSA and Ed25519) to authenticate transactions made by private key holders. A sufficiently advanced quantum computer could, via Shor’s algorithm, recover private keys from public ones, enabling unauthorized signature forging and fund transfers.
Not all components are equally vulnerable. Hash functions like SHA-256 and Keccak are far sturdier. Quantum search algorithms, such as Grover’s algorithm, provide a limited acceleration that can often be countered by increasing hash sizes and security parameters. The areas most likely needing future upgrades pertain to signatures, rather than to proof-of-work (PoW) processes or fundamental transaction integrity.
For blockchains, this necessitates comprehensive cryptographic enhancements to uphold expected security standards as they evolve.
Did you know? The term “Y2Q” is informally used to denote the year when quantum computers could significantly challenge traditional cryptography, akin to the “Y2K” scenario that concerned the year 2000. Some estimates have previously pointed to a 2030 timeline.
Why Quantum Security Just Jumped onto Layer-1 Roadmaps
While discussions around quantum risk have existed in scholarly settings for a considerable time, it recently gained traction as a tangible agenda item for layer-1 development teams. The pivotal moment came with the transition from concept to established standards and strict timelines.
From 2022 to 2024, NIST selected and began formalizing the first set of post-quantum algorithms. Among these are lattice-based techniques like the Cryptographic Suite for Algebraic Lattices (CRYSTALS)-Kyber for key establishment and Dilithium for digital signatures, accompanied by other alternatives like Stateless Practical Hash-based Incredibly Nice Collision-resistant Signatures (SPHINCS)+. This development provided engineers with a stable framework to plan around, rather than an ever-evolving research objective.
Simultaneously, governments and major businesses began addressing “crypto agility” and setting migration schedules for essential systems stretching into the 2030s. For public ledgers intended to safeguard values and contracts for decades, falling behind in this transition poses a governance challenge.
Layer-1 teams also respond to media coverage. Each significant announcement regarding breakthroughs in quantum hardware or research reignites debates about long-term security. Teams regularly contemplate whether their current signature mechanisms will remain secure throughout the lifespan of the network, and consider the advantages of establishing post-quantum options now rather than facing a forced transition later.
Did you know? The National Cyber Security Centre in the UK has recommended that organizations establish clear paths for upgrading to quantum-safe cryptography by 2028 and complete these migrations around 2035.
The First Wave: Which Layer-1 Networks Are Preparing
A select number of layer 1s have transitioned from speculation to tangible engineering efforts aimed at enhancing quantum resilience without disrupting existing functionalities.
Algorand: State Proofs and Live PQ Transactions
Algorand serves as a leading example of implementing post-quantum concepts. In 2022, it introduced State Proofs, which are concise certificates representing the chain’s history signed using FALCON, a NIST-selected lattice-based signature scheme. These proofs are quantum-safe and affirm Algorand’s ledger state at intervals of a few hundred blocks.
Recently, Algorand has shown its capability to conduct full post-quantum transactions on its main network with Falcon-based logic signatures, establishing itself as a potential quantum-safe validation hub for other blockchains.
Cardano: Research-First Roadmap to a PQ Future
While Cardano currently relies on Ed25519, its core teams and foundation regard quantum preparedness as a pivotal long-term asset. Founding member Charles Hoskinson recently discussed a comprehensive strategy encompassing a supplementary proof chain, Mithril certificates, and post-quantum signatures in line with NIST’s Federal Information Processing Standards (FIPS) 203 to 206. The goal is to add a quantum-resilient verification layer over the blockchain’s history instead of imposing a sudden transition for every user.
Ethereum, Sui, Solana, and “Quantum-Ready” Newcomers
On Ethereum, research teams have begun outlining a plan for post-quantum migration. This includes new transaction formats, rollup initiatives, and zero-knowledge-based wrappers that would enable users to add quantum-safe keys without needing to overhaul the underlying protocol instantly.
At the same time, Sui’s team has released a dedicated quantum-security roadmap, collaborating with academic partners to propose a transition pathway for EdDSA-based networks like Sui, Solana, Near, and Cosmos that avoids disruptive hard forks.
Solana has implemented an optional quantum-resistant vault utilizing hash-based one-time signatures to safeguard high-value assets, allowing users to store funds under more secure conditions.
Additionally, a series of newer layer 1 networks is marketing themselves as inherently quantum secure from inception, often incorporating post-quantum signatures into their base protocols. While these may be relatively small and untested, their emergence underscores the increasing importance of quantum readiness in how networks portray their long-term sustainability.
Did you know? The Quantum Resistant Ledger, launched in 2018, is one of the earliest dedicated blockchains designed with quantum resilience in mind, employing hash-based eXtended Merkle Signature Scheme (XMSS) signatures in place of standard elliptic-curve methods.
Under the Hood: Why Going Post-Quantum Isn’t a Simple Swap
Transitioning to post-quantum signatures might seem simple; however, implementing them on a live global network presents numerous challenges. The new algorithms operate differently, influencing everything from block sizes to user experiences in wallets.
The leading post-quantum candidates generally fit into three categories:
- Lattice-based signatures like Dilithium and Falcon, recognized by NIST, are rapid and efficient but often involve larger keys and signatures than traditional elliptic-curve schemes.
- Hash-based signatures such as SPHINCS+ depend on conservative assumptions, yet they can be bulky and, in certain variants, are limited to one-time use, complicating wallet functionality.
- Code-based and multivariate schemes are also significant for key exchange and specialized uses but have yet to become common in layer-1 strategies.
These design decisions have crucial implications for blockchains. Larger signatures result in heavier blocks, demanding greater bandwidth from validators and more storage in the long run. Hardware wallets and lightweight clients must handle more extensive data verification. Consensus processes are similarly affected, especially in PoS systems that depend on verifiable random functions or committee signatures, necessitating quantum-resistant replacements rather than merely introducing new keys for user accounts.
Moreover, there’s the challenge of transitioning. Substantial sums are locked in legacy addresses owned by individuals who may have lost access to their keys, passed away, or simply ceased engagement. Networks must decide how to approach the situation:
- Support hybrid signatures (classical plus post-quantum) to allow gradual user adoption.
- Create new transaction forms that incorporate quantum-safe schemes over existing keys.
- Or implement incentives and deadlines for rekeying longstanding dormant funds.
None of these choices purely involve technical considerations; they intersect with governance, legal treatment of assets, and the fate of coins owned by individuals who do not partake in the upgrade process.
What Users, Builders, and Investors Should Watch Next
Quantum risk doesn’t necessitate an immediate rush, but it redefines how various stakeholders evaluate the long-term reliability of a network.
For everyday users, the best initial step is paying close attention to discussions about crypto agility, which refers to the ability to incorporate and rotate cryptographic techniques without disruptive hard forks.
In the upcoming years, expect the introduction of new account types, hybrid signature options, and wallet notifications prompting key upgrades for high-value assets. The earliest implementations are likely to be seen in bridges, sidechains, and rollups before extending to the primary layer 1.
For developers and protocol architects, the focus should be on flexibility. Smart contracts, rollups, and authentication systems that are rigidly tied to one signature algorithm will soon become outdated. By designing adaptable interfaces and standards that can accommodate various schemes, both classical and quantum-safe, it becomes significantly simpler to comply with NIST and industry recommendations as they evolve.
For investors and governance participants, readiness for quantum vulnerabilities is evolving into an essential aspect of technical due diligence. Questions regarding throughput, data accessibility, or maximal extractable value (MEV) are no longer sufficient. The more profound inquiries are:
- Does this network have a documented post-quantum strategy?
- Are there functional prototypes or features such as state proofs, vaults, or hybrid transactions, or is it merely promotional rhetoric?
- Who will be responsible for making migration-related decisions when the time arrives?
If significant quantum attacks become feasible in the far-off future, networks that have modernized their cryptography will be better positioned within recommended security protocols.
Layer 1s that view quantum threats as gradual governance-level challenges and start constructing protective measures now are essentially wagering on the enduring relevance of their networks for decades to come.


